Most companies do not know where their secrets live. They have data in the cloud and data on local servers and data on mobile devices. An inventory of these assets is the first step toward safety. National institutes have finalized standards for new cryptographic tools. These tools rely on mathematical problems that even quantum machines find impossible to solve quickly.
Upgrading these systems requires a concept called crypto-agility. This means a system can swap one algorithm for another without crashing the entire network. It works like a universal adapter for digital safety.
We are winning that race.
Quantum processors utilize qubits to process data in parallel. RSA encryption depends on the math of prime factorization. Peter Shor developed an algorithm in 1994 that bypasses this hurdle using a quantum supercomputer. This capability threatens the privacy of bank transactions. It threatens the secrecy of government communications.
It threatens the integrity of the power grid. Engineers are currently deploying Module-Lattice Key Encapsulation Mechanism as the primary defense against this mathematical shortcut.
Transitioning the fiber-optic backbone requires hardware that supports larger key sizes. Most legacy routers lack the memory to store a post-quantum signature. Software developers are writing code that allows a system to operate in a hybrid mode.
This mode uses both RSA and lattice-based algorithms. If one layer fails, the other remains intact. I keep coming back to the fact that this upgrade is the largest cryptographic overhaul in human history. It succeeds because engineers are prioritizing backward compatibility during the rollout.
Satellite networks serve as the current frontier for this technology.
Optical ground stations transmit quantum keys through photons. This method creates a physical link that cannot be intercepted without changing the state of the particles. Cloud infrastructure leaders in Seattle have already enabled these protocols for corporations. The success of this rollout proves that the internet will survive the arrival of advanced computing.
We see the results in the safety of medical records. We see the results in the protection of financial logs. We see the results in the defense of the electrical grid.
Honestly? It’s not that simple because the physical infrastructure for quantum key distribution is expensive. A fiber optic cable can only carry these specialized signals for about one hundred kilometers before the data degrades.
Repeaters are needed. Specialized sensors are needed. Satellite relays are needed. Despite these costs, the investment protects the data that underpins the modern economy. This shift moves us from a world of “hopeful security” to one of “mathematical certainty.”
How did we reach here
The realization that current math would fail started in the 1990s. Research moved from theory to practical standards over three decades.
Governments realized that attackers were gathering data now to decrypt later. This pushed for immediate action.
Current Timeline:
- 1994: Publication of Shor’s Algorithm.
- 2016: NIST initiates the Post-Quantum Cryptography Standardization process.
- 2024: Official publication of FIPS 203 and FIPS 204.
- 2025: Browser vendors integrate ML-KEM by default.
- 2026: Global banking systems implement quantum-safe protocols for cross-border transfers.
Places of Interest:
Gaithersburg in Maryland serves as the headquarters for the cryptographic standards team.
Waterloo in Ontario hosts researchers focusing on the software transition. Hsinchu in Taiwan produces the semiconductors capable of running these new math problems.
Supplemental Material
Official Standards: NIST Post-Quantum Cryptography Project
Technical Implementation: Cloudflare Post-Quantum Readiness
Government Guidance: CISA Quantum Transition Roadmap

 AI Saves Human Workforce From Beer-Borne Illness, Boosts Productivity By 100%
AI Saves Human Workforce From Beer-Borne Illness, Boosts Productivity By 100%
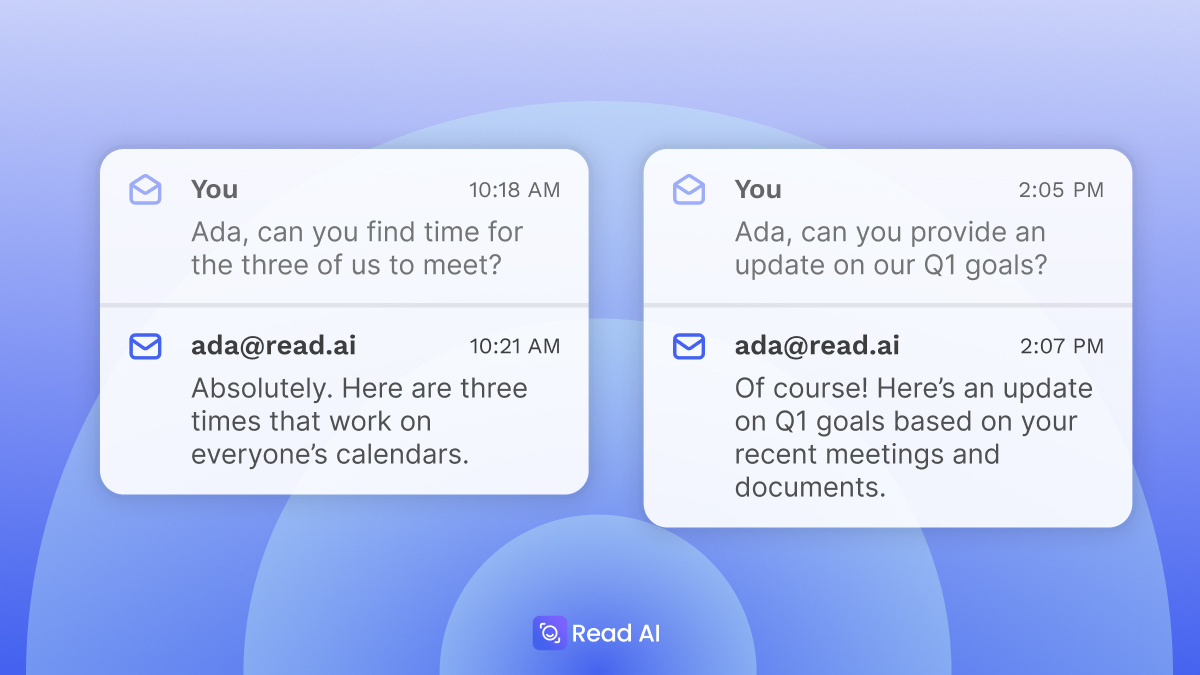 Microsoft And Google Just Announced AI-Powered Email Tools, But This New ‘Inbox Avatar’ Takes …
Microsoft And Google Just Announced AI-Powered Email Tools, But This New ‘Inbox Avatar’ Takes …